
1. Introduction
On April 1st, $285 million was stolen from Drift Protocol in 12 minutes. This is the largest DeFi hack of 2026, associated with Lazarus Group, North Korea’s state-sponsored cyber-crime unit.
The attack didn’t start on April 1st. It started six months earlier, at a crypto conference, with a handshake.
A group posing as a quant trading firm spent months building trust with the Drift team. They met in person across multiple countries and deposited over $1 million of real capital. When they had enough access, they tricked key signers into pre-approving hidden transactions, manufactured a fake token out of thin air and drained $285 million in real assets before anyone could react.
2. The Relationship
Drift is the largest decentralized perpetual futures exchange on Solana. At the time of the attack it held roughly $550 million in user assets. For an attacker, it was a high-value target with complex governance and multiple entry points.
The Approach
In the fall of 2025, a group presenting as a quantitative trading firm approached Drift contributors at a major crypto conference. Over the next six months they showed up at multiple conferences across several countries, building rapport with Drift team members.
They were technically fluent, had professional backgrounds and were familiar with how Drift worked. A Telegram group was set up after the first meeting, and months of substantive conversations followed about trading strategies and vault integrations.
Everything about this looked like a normal business partnership.
Between December 2025 and January 2026, the group onboarded on Drift. They deposited over $1 million of their own capital. They shared code repositories, tools, and applications they claimed to be developing. They asked detailed product questions across multiple working sessions. These interactions continued up until the attack.
Then right as the attack went live, the group’s Telegram chats and software were deleted.
The Twist
The people that Drift met in person were not North Korean nationals. DPRK threat actors used third-party intermediaries for face-to-face relationship building. The individuals had fully constructed identities with public-facing credentials.
Before Drift, the crypto industry treated meeting collaborators in person as a reliable filter. That filter no longer holds.
The Human Reality
Consider the perspective of a Drift contributor. You’ve met these people in person, multiple times. They’ve deposited real money into your protocol. They ask smart questions. They’ve seemed genuinely engaged for six months.
At what point do you stop verifying every interaction and start trusting?
3. The Setup
The Compromise
There are two suspected entry points.
One contributor likely got compromised after cloning a code repository shared by the group. Opening the project was enough to silently execute malicious code with no warning.
A second contributor downloaded a wallet app via Apple’s TestFlight, a platform for distributing pre-release apps that bypasses Apple’s normal security review. The group asked the contributor to beta-test it.
Once devices were compromised, the attackers had what they needed to obtain multisig approvals.
The Fake Asset
Three weeks before the attack, on-chain staging began. The attackers withdrew ETH from Tornado Cash and deployed a fictitious token: CarbonVote Token (CVT). They minted 750 million units, seeded a few hundred dollars of liquidity on Raydium, and used wash trading to maintain a price near $1.
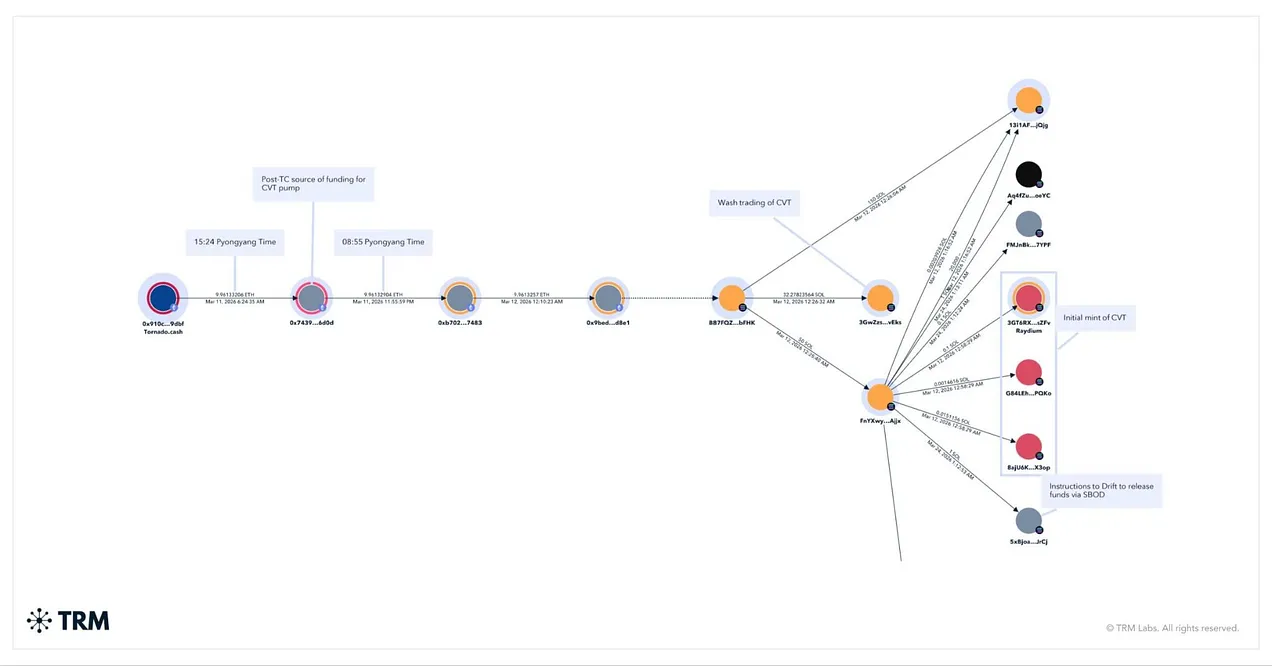
Over three weeks, this manufactured trading activity built a credible price history on a Switchboard oracle feed, one of the pricing services Drift relies on to value assets. The oracle did what it was designed to do: report the last traded price from on-chain exchanges. It doesn’t check liquidity depth, number of counterparties, or whether the trading is real. It just notes the price.
Think of it like this: someone incorporates a shell company, issues 750 million shares, and trades them back and forth with themselves until the stock shows a stable $1 price.
An automated pricing service marks the stock at $1 based on observed trades. The fake asset now had a real-looking price history, sitting in a live oracle feed, waiting to be connected to Drift.
The Pre-Loaded Trap
Drift uses a borrow/lend system. Users deposit collateral and borrow assets against it. This is how the attackers planned to extract funds: deposit fake collateral, borrow real assets.
But first they needed admin control.
Drift’s Security Council operated as a 2-of-5 multisig. Any two of five signers could authorize admin actions.
Solana has a legitimate feature called “durable nonces” that lets you sign a transaction today and execute it later without it expiring. This gave the attackers a way to collect signatures in advance and hold them until the right moment.
How the attackers obtained the multisig approvals is still under investigation by Mandiant. There are two likely paths.
- The malware delivered through the code repository and TestFlight app compromised the signers’ devices directly, allowing the attackers to extract keys or trigger signatures.
- The attackers presented misleading signing requests that looked routine but carried hidden admin authorizations, similar to what we saw with Bybit.
Either way, the outcome was the same. Pre-signed transactions sitting ready to execute whenever the attacker chose.
The Last Defense Removed
Five days before the attack, Drift migrated its Security Council to a new 2-of-5 multisig configuration with zero timelock. The migration was a planned operational change due to a council member changeover.
Timelocks create a mandatory delay between when a governance action is approved and when it takes effect. That delay is the detection window that gives the community or security team time to catch and reverse actions. Removing it meant that any two signers could authorize admin actions with immediate effect.
Whether this migration was influenced by the attackers through social engineering or was a coincidence they exploited remains under investigation. Either way, the attacker adapted in real time. They’d already compromised signatures on the old multisig. By March 30, three days after the migration, they had re-obtained 2-of-5 authority on the new configuration.
4. The Attack
April 1, 2026, 9am Pyongyang time. The pre-signed transactions deploy.
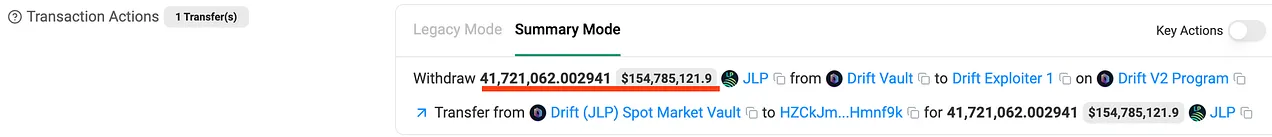
Two transactions, here and here, four Solana slots apart, were enough to complete the admin takeover. Within minutes the attacker had full control of Drift’s protocol-level permissions.
They used that control in rapid sequence: listed CVT as a new market with valid collateral, pointed its pricing at the Switchboard feed they’d spent three weeks manufacturing data for, raised withdrawal limits to extreme levels, and deposited hundreds of millions of CVT against the manufactured price.
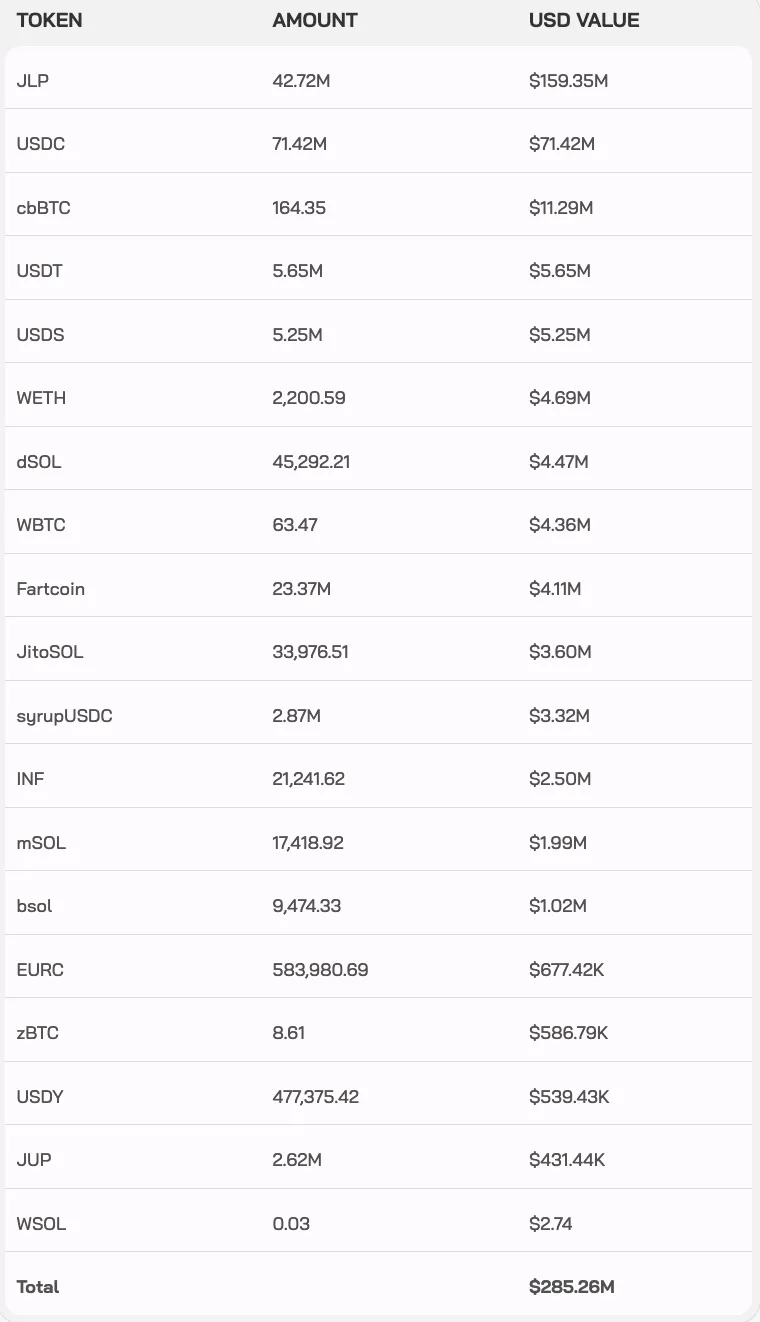
Then the borrowing began. The attacker used Drift’s own lending system to borrow real assets against the fake collateral. USDC, JLP tokens, SOL, wrapped BTC. The protocol processed every withdrawal as a legitimate collateral-backed loan. From its perspective, someone had deposited hundreds of millions in collateral and was borrowing against it. Standard operations.
Going back to our analogy: now the person who created the shell company took over the bank. They choose which pricing feed to trust, set the borrowing limits, and approve their own worthless shares as collateral. Then they borrow real money against them and walk out.
31 transactions in roughly 12 minutes. $285 million in real assets drained.
5. The Aftermath
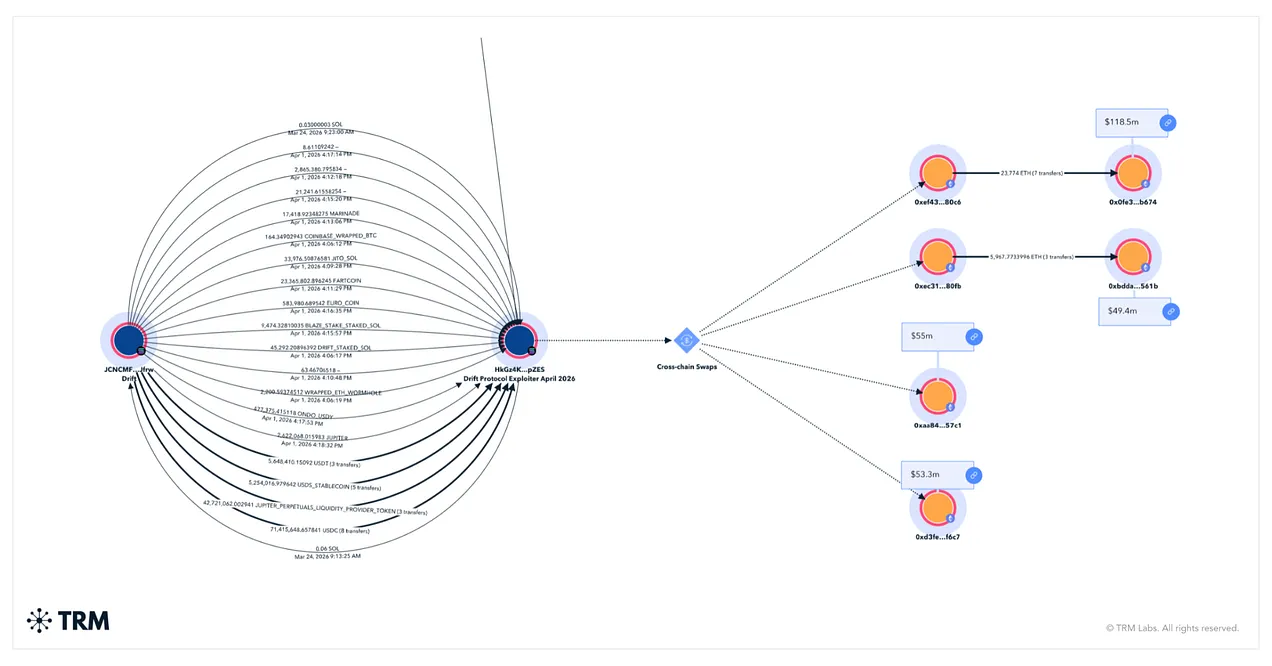
Where the Funds Went
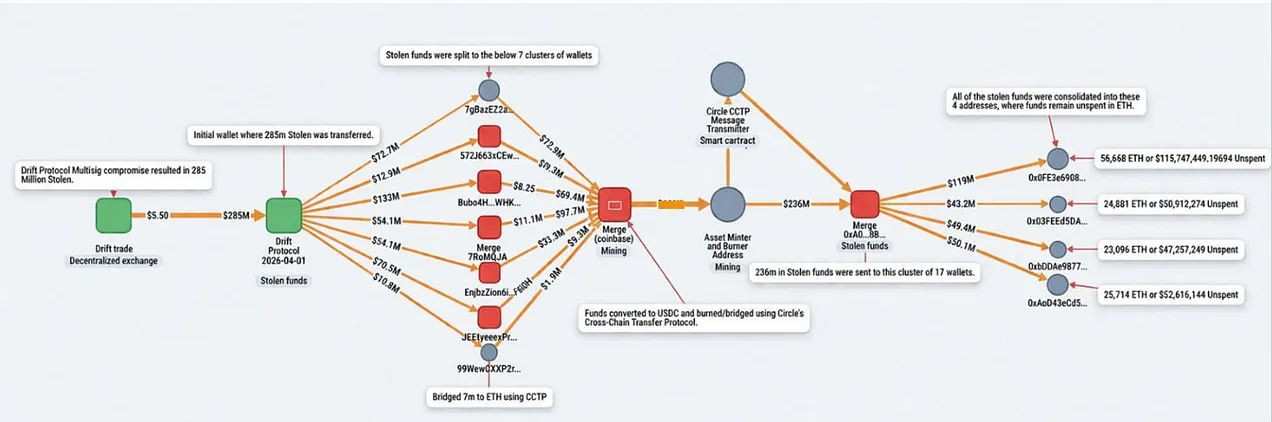
The stolen assets were consolidated and swapped into USDC and SOL, then bridged to Ethereum within hours using Circle’s Cross-Chain Transfer Protocol (CCTP). On Ethereum, portions were converted into ETH, accumulating roughly 129,000 ETH across attacker wallets.
The speed outpaced even the Bybit laundering operation in 2025. Lazarus has refined this playbook across multiple hacks: bridge assets across chains to break the transaction history, swap out of freezable stablecoins into ETH, then disperse.
Over $230 million in USDC was bridged across more than 100 transactions during US business hours. ZachXBT criticized Circle for not freezing the stolen USDC during the six-hour window after the attack began. Circle has stated it only freezes assets when legally required.
The Blast Radius
More than 20 Solana protocols with exposure to Drift liquidity paused operations or assessed losses. Some lost access to user funds entirely and will be forced to shut down.
In DeFi, the beauty is in creating “money legos”, linking protocols together to create new products. The peril is that every protocol becomes a counterparty and when one fails, the exposure cascades.
Attribution
Elliptic and TRM Labs attributed the attack to DPRK-linked actors. Fund flows trace back to the same group behind the $53 million Radiant Capital hack in October 2024. Over $6.5 billion has been stolen by DPRK-linked actors in recent years.
DeFi’s failures are directly funding nuclear weapon programs in North Korea.
6. The Connection
In February 2025, Lazarus stole $1.4 billion from Bybit by compromising a signing interface and hiding a malicious parameter inside a routine transaction. Employees approved it because the interface told them it was safe.
This time they came back with an even longer game. They targeted the employees themselves, over six months of conferences and working sessions. They deployed $1M of real capital as cover. By the time of the attack, the Drift team had no reason to question them.
Drift had passed multiple audits. But no code was compromised. A 2/5 multi-sig meant the attacker only needed to compromise two people to take full admin control with immediate effect. For a protocol holding $550 million in user assets, that threshold was too low and the safety net was missing.
7. Conclusion
Was the Drift hack preventable? That’s a harder question than it was for Bybit.
Some of the fixes are straightforward.
Signing devices should be isolated from day-to-day work machines. If the compromised contributors had used dedicated hardware for multisig approvals, separate from the laptops where they cloned repos and downloaded TestFlight apps, the malware would never have reached the keys.
Timelocks on admin actions are essential. Even a 24-hour delay on the governance migration would have created a window to detect and block the attack. A higher signing threshold, 3-of-5 or 4-of-5 for a protocol of this size, would have forced the attacker to compromise an additional person.
These are known best practices and should have been in place.
The scarier part is the nature of the attack itself. This was a con with 6 months of preparation. Real people at conferences, real money deposited. Every interaction designed to build trust so that when the moment came, the targets wouldn’t think twice.
If you’ve seen The Sting, you know how this works. You build an entire world around the target. Everything they see confirms what they believe. By the time the trap closes, they don’t even know they’ve been played.
In the film, the prize was $500,000. The Drift operation followed the same playbook for $285M. At those stakes, six months of preparation and a million dollars of cover is a rounding error. As more value moves on-chain, the cons will only get more elaborate.
No single control survives that. You need overlapping layers across code, people, and governance. Each one has to catch what the others miss. And when something is caught, the response has to be automated. Twelve minutes doesn’t leave time for a phone call.
Attacks like this won’t stop. But with layered controls and the ability to respond at machine speed, they don’t have to win.
The attack surface keeps expanding, from code to signing interfaces to the humans behind them, but the underlying problem remains the same: when something goes wrong, the window to respond is shorter than any human process can match.
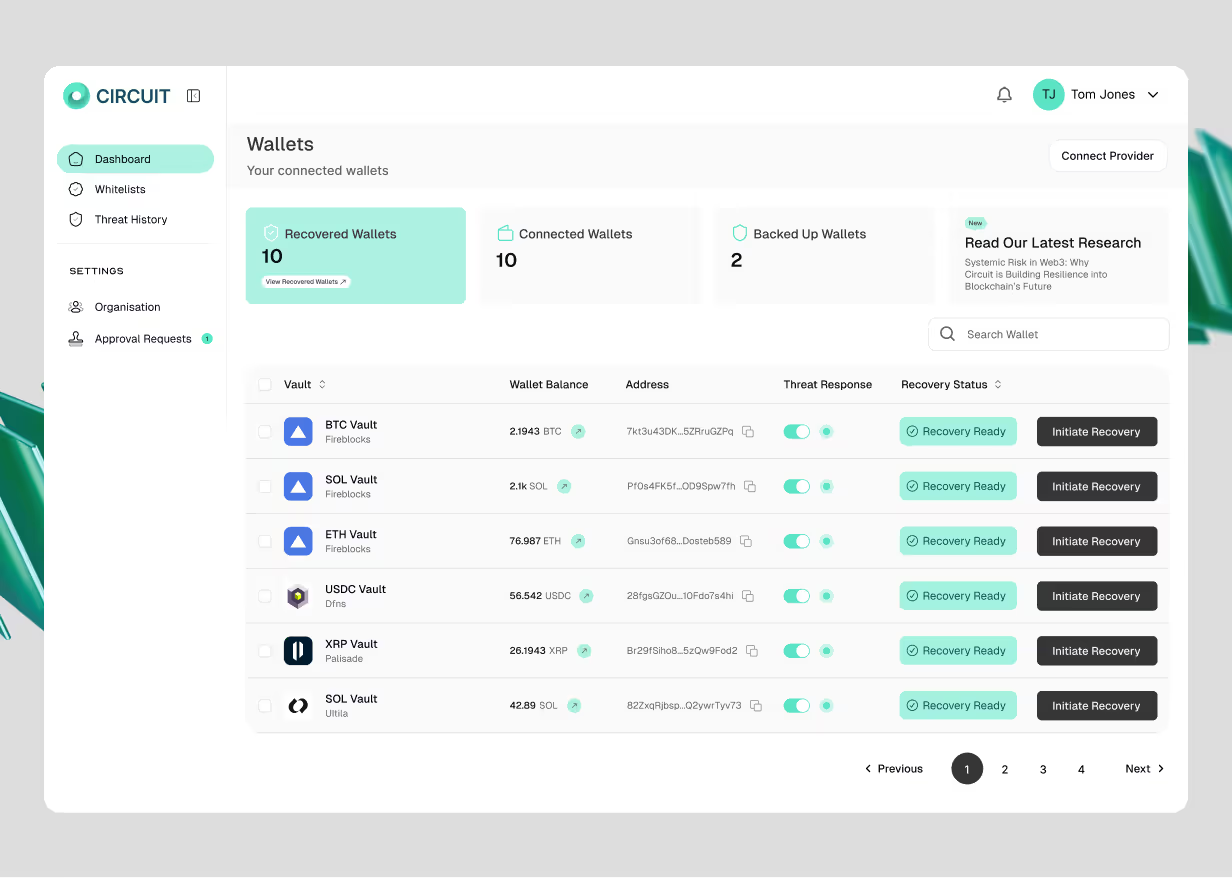
Circuit builds infrastructure for this scenario. Automated controls that move funds to safety when a threat is detected, without waiting for manual intervention. These are the kind of attacks our systems are designed to prevent.
Circuit is backed by Lloyd’s of London and recognised by 10+ major insurers as an enterprise risk control that reduces premiums. If you’re thinking about how to protect digital assets against attacks like this, we’re here to talk.
Want to keep up to date with Circuit? Sign up below
Related Posts
Discover more about Circuit’s latest News and Research
Inside the Kelp/LayerZero Hack: How Lazarus Forged $292M Into Existence
A single lie, six layers deep, and the cascade that pulled in every major lending protocol on Ethereum. A forged cross-chain message led to a $292M exploit draining Kelp and cascading into Aave and DeFi. This breakdown shows how one failure propagated across Ethereum.

What Google's Quantum Paper Actually Means for Crypto
The largest treasure hunt in human history is already underway. Google’s quantum paper cuts the timeline to break crypto security by ~20x. This guide explains the risks to Bitcoin, Ethereum, and $100B+ in digital assets.

The US Crypto Regulatory Convergence: What Compliance Teams Need to Know Now
Every major US federal financial regulator has moved to enable institutional crypto. The OCC's 376-page GENIUS Act rulemaking is the most operationally detailed framework yet, covering reserve requirements, redemption mechanics, custody standards, and operational resilience. We break down what the proposed rules require, where the compliance pressure points sit, and what operators should be doing before the comment period closes on May 1, 2026.
Built by experts who’ve made digital assets safer, and now, recoverable
We believe asset recoverability is table stakes for the next era of digital assets.





