1. Introduction
On April 18, Kelp’s Ethereum bridge released $292 million to an attacker. The largest DeFi exploit of the year.
The bridge checked every box on its internal list before handing the funds over. The signature was valid. The verifier watching the source chain confirmed the transfer had happened.
The problem was that none of it was real.
The verifier had been fed lies by infrastructure it trusted, manipulated by Lazarus Group, North Korea's state-backed cyber unit and the same actors who hacked Drift Protocol three weeks ago.
The theft was only the start. Within minutes, the attacker used the stolen funds as collateral on Aave and borrowed against them. By the time Kelp could freeze anything, the damage had escaped the bridge entirely. Aave was carrying ~$200 million of bad debt, WETH suppliers were locked out of their funds, and the cascade had pulled in every major lending protocol on Ethereum.
This piece walks through how one forged signature started a cascade which has impacted all of DeFi.
2. The Setup
What Kelp Is
Kelp is a liquid restaking protocol. Users deposit ETH, Kelp routes it through Ethereum staking and a secondary yield network called EigenLayer, and issues a receipt token called rsETH in return.
rsETH lives on more than 20 chains. Ethereum is the hub. Every other chain holds a wrapped version, a copy of the token backed 1:1 by real rsETH held in custody on Ethereum.
Custody Contract
When you bridge rsETH to a Layer 2 (L2) chain, your actual tokens don’t travel anywhere. They get deposited into Kelp’s custody contract on Ethereum, and an equivalent amount gets minted on the L2. Bridge back and the L2 version gets burned, releasing your original rsETH on Ethereum.
Think of it like this: the custody contract is a shared safety deposit box holding everyone’s rsETH. The L2 wrapped tokens are withdrawal slips against that box. Drain the box and every slip becomes worthless.
At the moment of the attack, the box held 116,723 rsETH.
How the Messages Are Verified
LayerZero is the messaging layer that connects these chains. It delivers instructions, it doesn’t hold funds. Think of it as SWIFT for blockchains.
LayerZero’s security rests on verifiers, a separate party that watches events on the source chain and attests to the destination chain that they actually happened. LayerZero calls them DVNs, for Decentralised Verifier Networks. The name is misleading. In practice, a DVN is typically a smart contract run by one operator with an internal multisig.
Applications pick how many DVNs they require. LayerZero’s own documentation recommends at least two.
Kelp’s Unichain-to-Ethereum path required exactly one.
That one verifier was operated by LayerZero Labs, the same team that built the messaging layer. It runs a 2-of-3 multisig: three signing keys, with two needed to approve any attestation, all held by one organisation.
When an application picks LayerZero Labs as its only verifier, the messaging layer and the verification layer collapse into the same party. Two signatures from the same firm do not become independent verification because there are two of them. One organisation ends up running both the roads and the traffic lights.
The attacker understood this, picked the weakest path, and walked through it.
3. Act 1: The Forged Message
The Pre-Stage
Ten hours before the attack, someone funded nine fresh wallets from Tornado Cash, a privacy tool that breaks the link between the source and destination of funds. All previously unused and loaded with roughly 0.098 ETH each.
The Transfer That Wasn’t
The attack took three transactions and two minutes.
At 17:33 UTC, a DVN admin submitted a signed attestation on Ethereum. The attestation said a transaction on Unichain had just asked Kelp to release 116,500 rsETH to a specific recipient address. The signatures matched the DVN’s authorised keys and Ethereum accepted the attestation.
Two minutes later, the attestation entered into Ethereum’s official record, marking the message as verified and ready to execute.
Thirty seconds after that, the attacker called the execute function. Ethereum performed its one check: did this incoming message match the verified attestation? It did. The instruction passed to Kelp’s custody contract, which decoded the message and transferred 116,500 rsETH to the recipient.

From Ethereum’s perspective, everything worked exactly as designed.
The Impossible Math
But there was a problem.
Every EVM-chain transaction carries a nonce, a counter that tracks transaction order for each account. Nonces go up by one. They can’t be skipped or reused. If Kelp’s Unichain contract had genuinely sent a transfer message, its nonce would have advanced.
It didn’t. The Unichain outbound nonce stayed stuck at 307 throughout. It never advanced to 308.
No source-chain transaction ever happened.
The rsETH total supply on Unichain stayed at 49 tokens, unchanged across the entire attack window.
A legitimate burn of 116,500 rsETH was impossible.
Ethereum released user deposits against a transfer message nobody had ever sent. The signature proved someone authorised to sign did sign. It did not prove anyone had actually watched Unichain before signing.
What Actually Happened
The DVN’s job was to watch Unichain. To do this, it relied on RPC nodes, servers that index blockchain data and answer questions about what’s on-chain. The DVN’s RPC nodes are its eyes.

Days before the attack, Lazarus Group had compromised two of LayerZero Labs’ RPC nodes deeply enough to replace the software running on them. The replacement binaries were surgical. They showed the DVN a forged transaction record. They told every other observer the truth. LayerZero’s monitoring systems saw nothing unusual because they were watching the same nodes and getting honest answers.
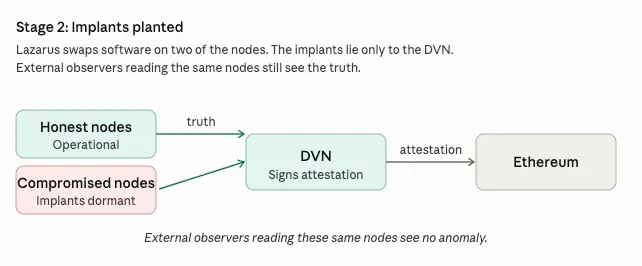
When the attack began, Lazarus launched DDoS attacks on the honest RPC nodes to take them offline. The DVN’s failover kicked in and it started reading from the only nodes still answering: the compromised ones. Those nodes told it a fake Unichain transaction had happened. The DVN signed.

The signing keys were not stolen. The DVN did exactly what it was designed to do. The deception happened one layer below, in the infrastructure the DVN trusted to tell it the truth.

Once the attack completed, the malicious binaries were designed to self-destruct, taking the evidence with them.
LayerZero’s post-mortem explains what the implants did. It has not explained how Lazarus got root access to the RPC nodes in the first place. That entry vector is the part of the story still open.
The Response
Forty-eight minutes after the first drain, Kelp’s multisig executed an emergency freeze. The rsETH token contract was paused. Transfers to the attacker’s recipient wallet were blocked.
By then, a second forged message had already been verified on Ethereum, queued to release another 40,000 rsETH worth $100 million. The freeze was the only thing stopping it. The message still sits on Ethereum today, verified and undelivered.
Forty-eight minutes is fast for human incident response. DeFi moves faster than that. What happened inside those forty-eight minutes is Act 2.
4. Act 2: The Cascade
The Attacker Now Had a Problem
At 17:35 UTC, the attacker held 116,500 rsETH. They now needed to convert them into something spendable, before the alarm went up.
Dumping them on decentralised exchanges was the obvious move. But rsETH secondary liquidity was thin. Selling 18% of circulating supply onto open markets would have crushed the price before the attacker could exit.
Aave offered a better exit.
How Aave Became the Exit Ramp
Aave is the largest lending protocol in DeFi. Users deposit tokens to earn yield. Others borrow against collateral they post. An oracle tracks market prices and tells Aave what each token is worth.
The attacker could post the stolen rsETH as collateral, borrow WETH against it, and walk away with liquid ETH without ever touching the rsETH market. WETH trades everywhere. Aave’s oracle would price the stolen collateral the same way it priced the legitimate kind.
Better yet for the attacker, Aave had been running rsETH in an efficiency mode, a setting for assets that move together. Correlated tokens let borrowers take higher leverage between them. The mode let users borrow 93 cents of WETH against every dollar of rsETH collateral.
The assumption was that rsETH would track ETH closely. That assumption holds under normal market conditions. It breaks entirely when the rsETH backing disappears.
Aave priced rsETH as though its security was rsETH security. It was actually the security of Kelp’s bridge configuration, held together by LayerZero Labs’ signing keys.
Test-Then-Scale
The attacker didn’t commit the full amount straight away. They ran tests.
1 rsETH supplied first. Then 5,000. Then 20,000. Then 27,999. Then 400.

Each step was a probe. Did any circuit breakers fire? Did the oracle refuse to price the new supply? Did a risk manager notice? When each step cleared, the attacker committed more. The attacker used them to confirm Aave’s parameters weren’t about to catch up with them.
Running in Parallel
Six other branches moved simultaneously.
Some repeated the Aave play at smaller size. Some used Compound and Euler instead. Some swapped rsETH directly for ETH through exchange aggregators. Some bridged rsETH to Arbitrum and ran the same Aave strategy against Arbitrum’s deployment.
Total debt extracted across Aave, Compound and Euler: ~$236 million.
The Position Nobody Would Close
When a borrower’s collateral on Aave falls in value, liquidators, third parties paid to close risky positions, step in. They repay the debt and take the collateral at a discount. The mechanism keeps the protocol solvent when borrowers default.
For the attacker’s position, nobody showed up.
The oracle, which updates on a delay, continued marking rsETH near its pre-attack price even though the real market was collapsing. Kelp paused redemptions, so nobody could unwind rsETH back into underlying ETH. Liquidators faced two options, neither workable: close the position at the oracle price and buy rsETH they had no way to sell, or close it at the real price and take an immediate loss on what they paid.

The position sat. Aave’s WETH pool hit 100% utilisation, meaning every available WETH had been borrowed. Every supplier trying to withdraw was blocked.
The Contagion
Aave’s total value locked fell from $26.4 billion to roughly $20 billion within 24 hours. Over $5 billion of ETH walked out. The AAVE token dropped 16%.
Other lending markets froze rsETH within hours. SparkLend, Fluid and Upshift shut down new activity. Lido paused deposits into its earnETH product because of indirect rsETH exposure. Ethena paused its own LayerZero bridges despite having no rsETH exposure.
The combination of one verification failure, one bridge configuration, and one lending market parameter started a cascade which is still ongoing.
5. Where We Currently Stand
The attacker’s Ethereum wallet holds 75,700 ETH. It has not sent a single transaction since the money arrived. A second wallet on Arbitrum holds another 30,700 ETH equivalent, equally untouched. Every analytics firm can see them. Nobody can freeze them. They sit, waiting, until the attacker decides to cash out.
Kelp’s contracts remain paused. The leveraged Aave positions on both Ethereum and Arbitrum remain open, carrying tens of thousands of rsETH as collateral against loans nobody can liquidate. At current prices, Aave is now carrying somewhere between $177 and $196 million of bad debt it cannot recover through normal mechanisms.
The protocol has an insurance-style backstop called Umbrella, which holds around $50 million of staked WETH designated to absorb exactly this kind of loss. Umbrella is queued to be slashed for the first time in its existence. The gap between what it covers and what was actually lost flows to ordinary WETH suppliers as a haircut.
Kelp has not published a recovery plan for bridged rsETH holders. Tokens on 20+ chains now have uncertain backing. The protocol’s ability to honour redemptions at full value depends on whether any portion of the stolen funds can be recovered.
Attribution is now confirmed. LayerZero has identified the attackers as Lazarus Group’s TraderTraitor subgroup. The same actors behind the Drift exploit three weeks ago.
The story isn’t done. We’ll cover the aftermath in a follow-up once the dust has settled.
6. The Broader Lesson
When Aave listed rsETH as collateral, it was implicitly underwriting every upstream dependency that kept rsETH backed. The actual stack looked like this:

- Aave trusted rsETH to be backed
- rsETH was backed by Kelp’s custody contract
- Kelp’s custody contract trusted LayerZero’s DVN to verify cross-chain messages
- LayerZero’s DVN trusted its RPC nodes to report what happened on-chain
- LayerZero’s RPC nodes trusted their own software to run correctly
- The software was replaced with a lie
Every layer trusted the layer beneath it. The attack broke the system three steps below the contracts. Nobody was looking there because nobody had thought to.
None of that stack appeared anywhere on Aave’s books. The risk it created ended up on the loan book regardless.
One compromised pair of servers should not be able to drain a custody pool holding hundreds of millions. It was able to because Kelp accepted a single-verifier configuration, because LayerZero’s architecture permits that configuration, and because Aave accepted the resulting token as high-leverage collateral without fully pricing what that token’s backing depended on.
Every tokenised or bridged instrument carries the security of its weakest upstream step. Until Saturday, that property was implicit in every liquid restaking token listed on every lending protocol in DeFi. Now it’s explicit.
7. The Speed Gap
Kelp’s freeze came 48 minutes after the first drain. For a weekend human response, involving multisig coordination and emergency contact chains, that’s fast. Most incident response teams would envy it.
In those 48 minutes, the attacker moved roughly $196 million of stolen rsETH into Aave, executed seven parallel strategies, and set up leveraged positions on two chains that cannot now be unwound.
Every attack in 2026 is happening at machine speed. Every response is still happening at human speed. The gap is where the money goes.
Circuit builds for this gap. Automated asset extraction that moves funds to safety when funds are compromised, before a human team can log in. Backed by Lloyd’s of London and recognised by 10+ major insurers as an enterprise risk control that reduces premiums.
Somewhere, the attacker is waiting. We'll cover their next move, and the damage Kelp and Aave are still working through, in the follow-up.
Want to keep up to date with Circuit? Sign up below
Related Posts
Discover more about Circuit’s latest News and Research

$285M Drift Hack Breakdown
A single lie, six layers deep, and the cascade that pulled in every major lending protocol on Ethereum. A $285M DeFi hack executed in 12 minutes after 6 months of social engineering. This breakdown shows how Drift was compromised and what it means for crypto security.

What Google's Quantum Paper Actually Means for Crypto
The largest treasure hunt in human history is already underway. Google’s quantum paper cuts the timeline to break crypto security by ~20x. This guide explains the risks to Bitcoin, Ethereum, and $100B+ in digital assets.

The US Crypto Regulatory Convergence: What Compliance Teams Need to Know Now
Every major US federal financial regulator has moved to enable institutional crypto. The OCC's 376-page GENIUS Act rulemaking is the most operationally detailed framework yet, covering reserve requirements, redemption mechanics, custody standards, and operational resilience. We break down what the proposed rules require, where the compliance pressure points sit, and what operators should be doing before the comment period closes on May 1, 2026.
Built by experts who’ve made digital assets safer, and now, recoverable
We believe asset recoverability is table stakes for the next era of digital assets.





