
Intro
This week, Google made headlines around the world. Every major publication reported the same thing: the security protecting Bitcoin is going to be broken sooner than anyone expected.
The headlines are bold. But the details are hard to check as they’re spread throughout a dense 57-page paper that covers advances in quantum computing, cryptography, blockchains, property rights, and national security policy all at once.
This piece breaks it down for you, step by step.
It’s a guide through how blockchain security works, how quantum algorithms can break it, what the advances in the paper mean, the risks the crypto ecosystem faces and how to deal with the coming threats.
Why do those things matter? Because underneath the technical complexity, this is the story of hundreds of billions of dollars in digital assets that will become accessible to whoever builds the machines that cracks the codes first.
The largest treasure hunt in human history is happening. Most people don’t know it yet.
2. The Lock
Every crypto wallet is protected by Elliptic Curve Cryptography (ECC), a type of mathematical problem that’s been considered so secure it’s used for securing almost everything critical, from internet traffic, to financial data, to personal data and much more.
It works by having two keys. A private key that only you know and a public key derived from it and shared openly. When you transact, you sign with your private key. The network verifies using your public key.
Think of it like a padlock. Your private key is the combination. Your public key is the closed lock. Snapping it shut takes a second. But if someone hands you the closed lock with no combination, the only way in is to try every number until one works.
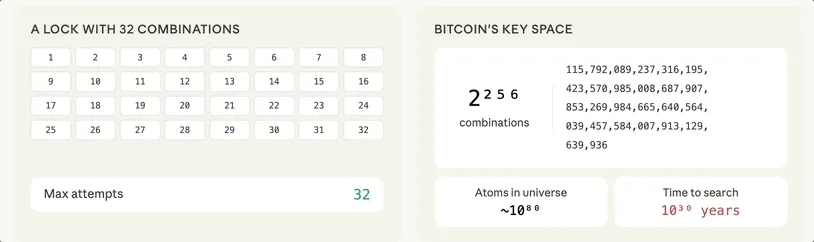
For Bitcoin that’s 2²⁵⁶ possible keys, a number so large that even if you used every computer on earth, working through all the possible combinations would literally take longer than the age of the universe.1
That’s why ECC has been considered so safe. Because classical computers can’t find the answer without stepping through an impossibly large sequence. But quantum computers can.
3. The Codebreaker
Richard Feynman, one of the founding fathers of quantum physics, famously cracked classified safes at Los Alamos during the Manhattan Project.
He studied the Mosler safes and found that because of how they were manufactured, there was a hidden weakness. The mechanical structure allowed him to feel the mechanism responding as he turned the dial.2 Once he got enough information from that, the number of possible combinations collapsed and he could walk through them all in just a few minutes.
It looked like magic from the outside but was just a different technique that exploited structure the lock’s designers thought was inaccessible. A hidden door that was invisible until you knew how to look.
It turns out the lock behind cryptocurrencies has the same kind of weakness. The algebraic structure of the elliptic curve connects every public key to its private key.
It’s part of the structure of the underlying maths. The designers knew it was there. But because exploiting it with a classical computer would take longer than the age of the universe, it wasn’t considered a risk.
Until someone built a different kind of computer.
Quantum Computers
A classical computer uses bits. Each bit is either 0 or 1. It works through possibilities one at a time.
A quantum computer uses qubits. A qubit it carries a blend of both 0 or 1, weighted by hidden numbers called amplitudes. You only get a definite answer when you measure it.
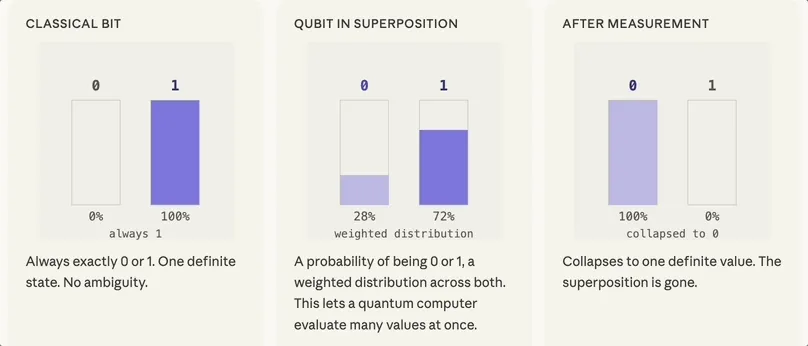
A single qubit in superposition isn’t useful. But string enough of them together and something emerges. Each qubit’s state becomes linked to the others, so the system as a whole holds far more information than any individual qubit holds.
Every qubit you add doubles the number of possibilities the system can represent. Scale that up and you quickly reach numbers that dwarf anything in the physical universe. This is what makes quantum computing fundamentally different.
But scale alone doesn't solve anything. If you measured this state, you'd get random noise. The breakthrough is in what you do between setting it up and measuring it.
Shor’s Algorithm
In 1994, mathematician Peter Shor found the breakthrough. He developed an algorithm to extract the private key directly from the public key.
It works in two steps.
Step 1: It recreates the same mathematical process that produced the public key from the private key but inside a quantum system. The private key leaves a hidden pattern in how that math behaves. The correct answer is in there, but it’s buried deep and indistinguishable from noise.
Step 2: It applies a calculation called the Quantum Fourier Transform. Think of it like Feynman being able to feel the mechanism responding as he turned the safe dial, it probes the hidden structure to extract otherwise invisible information. The wrong answers cancel each other out while the right answer reinforces itself. The noise turns into a single clear signal.
Once you measure this, the private key is whats left.
For thirty years, Shor’s algorithm has been a theoretical curiosity. A proof that quantum computers could break public key cryptography, if they ever became powerful enough.
That if is what Google’s paper is now closing.
4. Theory to Practice
Shor’s algorithm has existed since 1994. The reason it hasn’t broken Bitcoin yet is simple: nobody has built a machine powerful enough to run it.
To run Shor’s algorithm you need large numbers of qubits working together. The problem is that qubits are extraordinarily fragile. The slightest interference, such as heat or vibration, causes them to collapse and destroys the calculation.
To compensate, engineers combine many physical qubits together to produce one reliable logical qubit, an approach called quantum error correction. It works, but it’s expensive and is the reason why the qubit requirements seem so impossibly large.
Google’s most advanced processor, the Willow chip, has 105 physical qubits. The previous best estimate for the number needed to break Bitcoin’s cryptography was 9 million,3 almost 5 orders of magnitude larger. Thats why it seemed like a distant threat.
Exponential Progress
That distance is closing faster than people are expecting. Over the last fifteen years, the estimate of how many qubits a quantum computer would need to break widely used encryption has dropped exponentially. Figure 3 from the paper shows this trend for RSA-2048, another widely deployed cryptographic system. The trend for ECC protecting Bitcoin is similar.
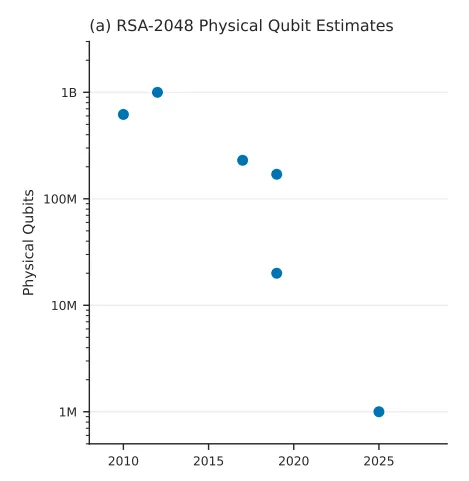
Those drops don’t come smoothly. The paper uses the car industry as an analogy. The late 19th century saw rapid innovation across steam, electric, and internal combustion engines all competing simultaneously. Progress came in sudden jumps as each architecture hit breakthroughs. Eventually combustion became the dominant design and progress shifted to gradual improvement.
Quantum computing is still in that first stage. There are multiple hardware architectures competing and progress is coming in sudden jumps as scaling challenges are overcome.
This paper is about one of those jumps.
The Finish Line Moves Closer
The previous best estimate for breaking Bitcoin’s elliptic curve cryptography, the 2²⁵⁶ combination lock we explored in Section 2, put the physical qubit requirement at around 9 million. The breakthrough here is that Google’s team brought that down to fewer than 500,000.
They got there by finding a more efficient way to compile the quantum circuits that run Shor’s algorithm. Prior work had optimised either for fewer qubits or for fewer operations, but not both together. This paper found configurations that kept both low simultaneously, leading to a ~20x reduction in estimated difficulty.
That 500,000 qubits figure is the output of several compounding engineering assumptions; a specific hardware architecture, qubit connectivity, error rates consistent with hardware Google has already demonstrated, and a particular error correction approach.
More aggressive assumptions could push the number lower. The researchers assert they chose assumptions that are reasonable to try to demonstrate the most credible near-term engineering path, not the most alarming one.
How Google Published It
One of the most interesting parts of the paper is what is absent. Google didn’t publish the actual circuits behind their result.
They used a zero-knowledge proof instead, a cryptographic technique that lets anyone verify the claim exists without being able to replicate it. That allows them to prove their result but not reveal exactly how they did it.
This breaks the academic tradition of full transparency. The reason they give is that publishing full attack details is now a public safety risk.
It’s a significant change to recognize that this cutting edge of research is now at a point where it’s of such importance and has such monetary incentives attached to it that we can’t rely on public channels to really know where the edge is. What is public information from now on will likely lag behind what is private.
5. From Sci-Fi to Science to Engineering
My read of the core idea that the researchers are trying to transmit from this paper is that right now many people treat the possibility of a quantum attack as hand-wavy science fiction. Maybe one day there will be a machine powerful enough to crack the encryption protecting everything we think is valuable. But it’s so far away that you don’t have to think about it.
That’s a view the researchers think is dangerous.
The Shift
Shor’s algorithm has existed since 1994. Bitcoin was built knowing the theoretical vulnerability was there. For decades, the gap between theory and practice was so large that the threat could be safely ignored as the engineering seemed impossibly far away.
A cryptographically relevant quantum computer (CRQC) is the term used to describe a machine powerful enough to run these attacks at scale.
What this paper actively showcases is that the engineering behind a CRQC is no longer impossibly far away. It’s becoming a clear problem with specifications, components in development, and multiple independent tracks of progress converging simultaneously.
When multiple components of an engineering challenge can improve independently, progress compounds. Papers announcing better algorithms, better hardware, better error correction are becoming more frequent as each improvement enables the next.
Acceleration
The number of qubits we can build is rising and the number of qubits we need to run these algorithms is dropping by orders of magnitude. Those two curves are converging, and the main point the authors of the paper is that they will meet sooner than most of the world is expecting.
Humans tend to think in straight lines. When progress compounds exponentially, human intuition fails. We consistently underestimate how quickly things can change as the curve accelerates.
Using a zero-knowledge proof to publish the results explicitly announces this danger.
A CRQC is becoming an engineering problem. Quantum attacks could come sooner than almost anyone expects.
6. What’s Actually at Risk
So we now know a CRQC is closer to being built than anyone expected and we know what it can do. The next question is what it could actually take.
6A. Bitcoin
Bitcoin’s quantum security comes down to one question. Is your public key visible?
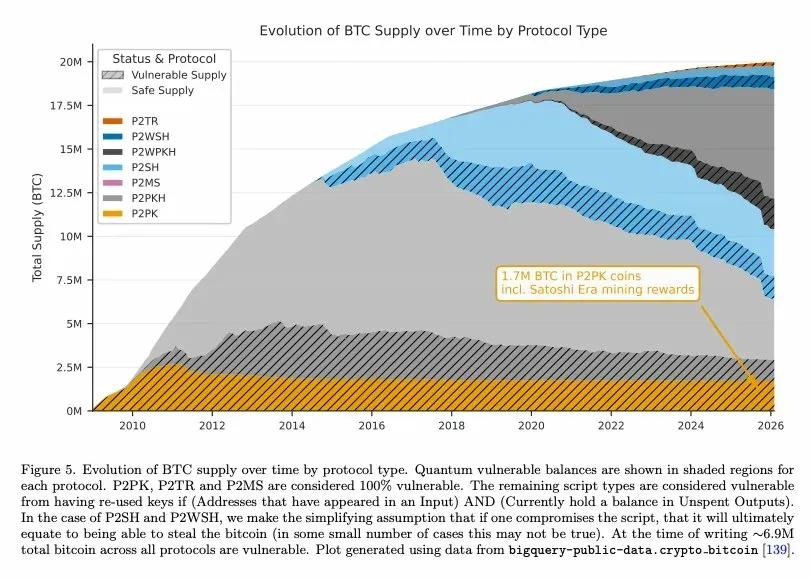
For every Bitcoin wallet this depends on something called a script type, a format that determines how funds are locked and how they can be spent. Different script types handle public key visibility differently. Some expose the public key permanently from the moment funds are received. Others keep it hidden entirely until a transaction is broadcast.
The chart below maps the full Bitcoin supply against each script type, with vulnerable portions shaded. Around 6.9 million BTC across all script types are currently vulnerable, about a third of all Bitcoin ever mined. At current prices that’s roughly $460 billion.
At-Rest Attacks
At-rest attacks target addresses whose public keys are already known or visible on chain. This is the 6.9m BTC mentioned earlier. An attacker with a CRQC has as much time as they want to derive the private key. There are three ways this exposure happens:
1. Weak address vulnerability. Certain script types record the public key directly on chain from the moment funds are received. The oldest of these, P2PK, secures around 1.7 million BTC which has had its public key visible since it was first mined, including Satoshi’s original mining rewards. The bitcoin remains vulnerable until it is spent.
2. Address reuse vulnerability. Script types that normally hide the public key behind a cryptographic hash become vulnerable when some but not all of the bitcoin at an address is spent. The spending transaction reveals the public key, defeating the protection the hash normally provides. Any remaining bitcoin at that address is now permanently exposed. The vulnerability arises entirely from reusing the same address to receive funds multiple times. Avoiding address reuse already is considered best practice in Bitcoin. Under quantum, it moves from recommendation to critical defence.
3. Offchain exposure. A public key can be revealed through activity elsewhere. Spending from the same key on another chain like Bitcoin Cash, or sharing a public key with third party service permanently exposes it. The attacker doesn’t need to wait for a transaction as the key is already out there.
At-rest attacks are serious but mitigable. Move funds to an address that hasn’t exposed its public key and the vulnerability disappears.
Unfortunately, there’s another type of attack category which is harder to escape.
On-Spend Attacks
On-spend attacks target every wallet, not just exposed ones.
When you broadcast a transaction, there’s brief window when a public key becomes visible in the mempool, the waiting area for transactions before they get confirmed and settled on-chain.
Every single Bitcoin transaction, regardless of script type, exposes the public key in the mempool. The moment you hit send, a vulnerability window opens. If an attacker with a CRQC can derive your private key before the transaction is confirmed, they can steal the funds.
Headline Number
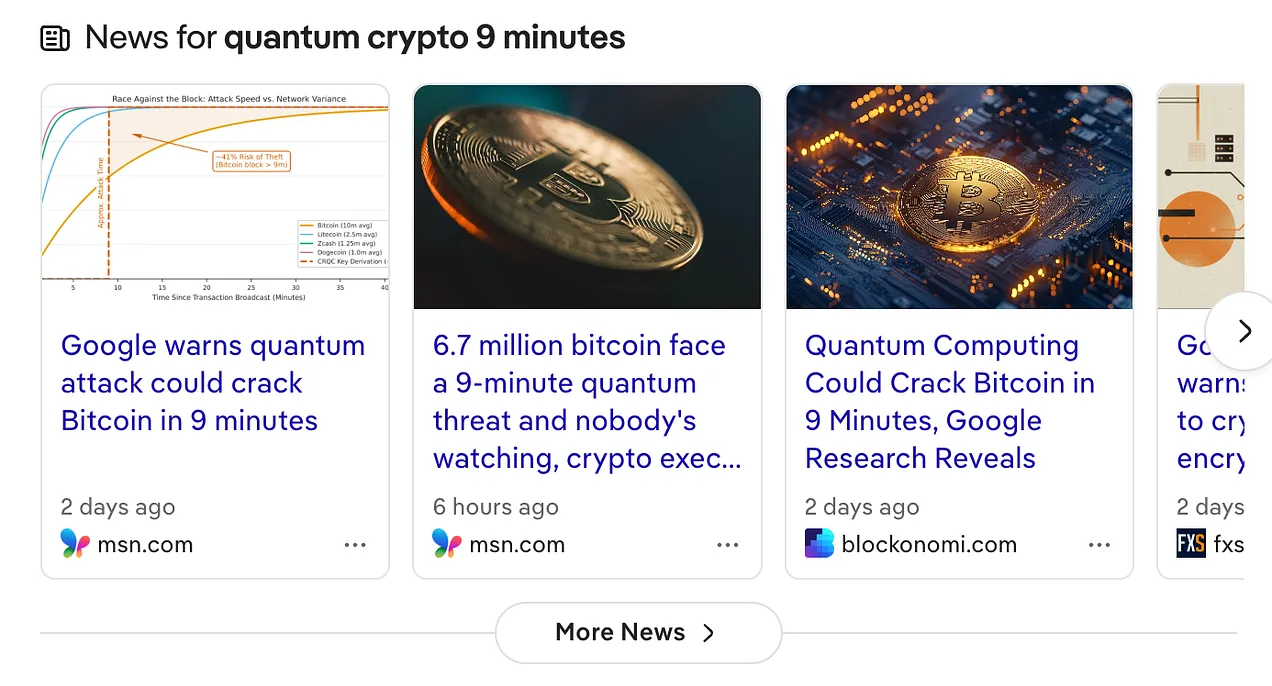
Bitcoin’s average block confirmation time is 10 minutes. The paper models, under several compounding assumptions, that a CRQC could complete the derivation in around 9 minutes. Under those same assumptions, they estimate a roughly 41% probability of success per transaction.
Those specific numbers are illustrative rather than predictive as they’re built on a stack of assumptions about hardware architecture, gate speed, and error rates. What matters is what they demonstrate: once a machine of this scale exists, the mempool window becomes an active vulnerability for every transaction on the network.
Blockchains with shorter confirmation windows look safer today. Litecoin’s 2.5-minute block time drops the current probability below 3% according to the paper.
But that safety is a temporary illusion. Bitcoin will be first in the crosshairs because of its 10-minute window. Everything else will follow as the hardware improves and by then it will happen quickly.
Proof of Work: Safe for Now
Bitcoin’s mining mechanism is not meaningfully threatened by current quantum advancements. Mining relies on hash functions, which quantum computers can attack using a different algorithm that provides a much more limited speedup than Shor’s. At current estimates, this doesn’t pose a practical threat to Bitcoin’s PoW security.
The paper does note an indirect risk. A quantum attack on wallets that caused significant market disruption could reduce mining profitability, causing hashrate to drop and then making the network more vulnerable to attack to reorganisation attacks from a well-resourced actor.
6B. Ethereum and RWA
Ethereum can run programs using smart contracts alongside acting as a ledger.
These programs govern lending, trading, stablecoins, and an increasing share of real-world financial assets. That makes Ethereum’s attack surface much wider. In Bitcoin, a quantum attack compromises a wallet. In Ethereum, it can compromise infrastructure with dependencies that ripple out across the entire ecosystem.
Accounts
From your first transaction, your public key is permanently tied to your account address on chain. Every active Ethereum account with a transaction history is an at-rest target.
Admin Keys
Most major smart contracts are controlled by admin keys. They exist because protocols need to be managed. And because they’ve been used in past transactions, their public keys are on chain.
Deriving an admin key can compromise everything that key controls.
I’ll use USDT and USDC to illustrate a clear example. Together they powered the majority of the trillions of stablecoin volume in 2025. A quantum attacker who derives their admin keys could mint as many tokens as they wanted, backed by nothing. An unlimited mint would cause the $1 peg to break. That broken peg cascades across every protocol that holds, prices, or settles against those assets. What starts as a cryptographic attack ends as a market collapse.
Beyond stablecoins, the combined value of assets locked across Ethereum’s ecosystem is around $200 billion4 and is continuing to grow.
As more real-world assets move on chain, more tokenized bonds, funds, and financial instruments come under the same vulnerability. Every asset that moves on chain before a solution is in place expands the surface that a CRQC could reach.
Consensus Vulnerability
Ethereum uses Proof of Stake, where validators secure the network by locking up their own ETH as collateral. There are currently around 37 million ETH staked. Validators authenticate their work using BLS signatures, a type of digital signature vulnerable to Shor’s algorithm.
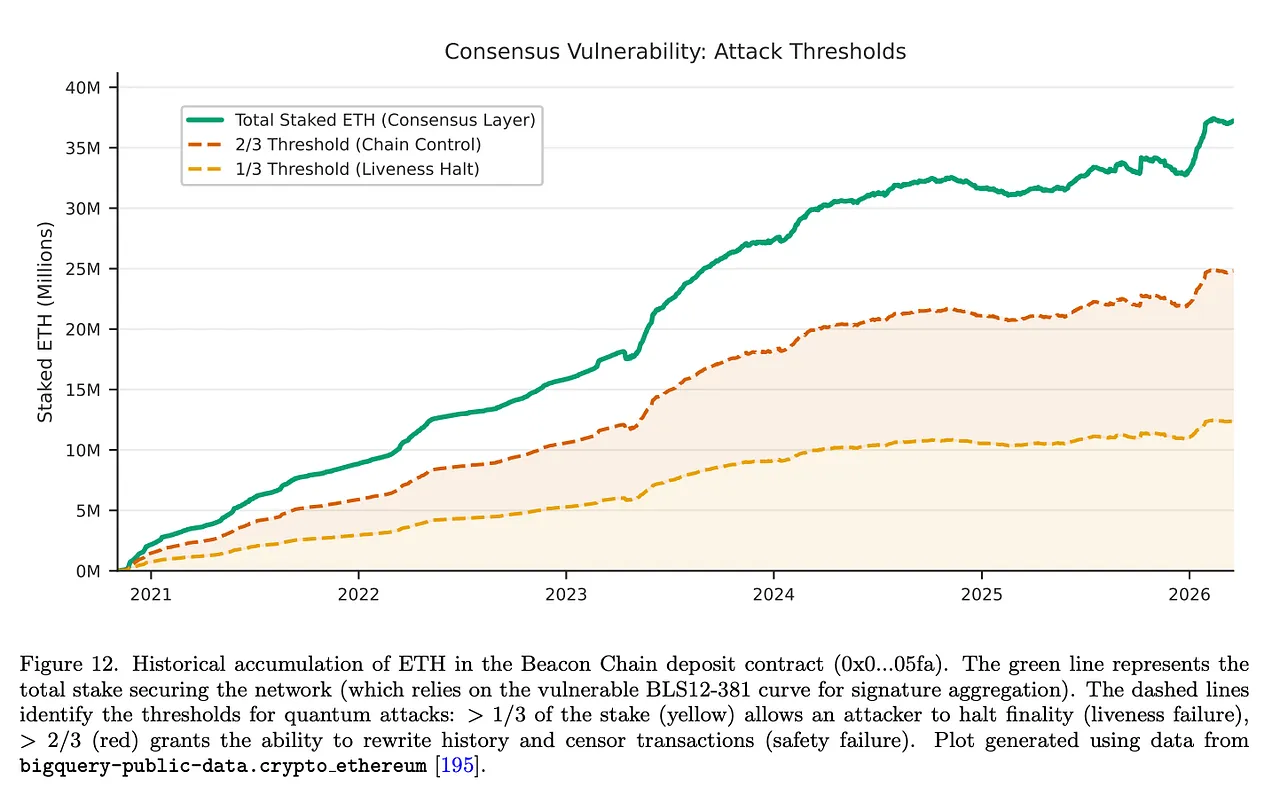
A CRQC that derives a validator’s signing key can not only steal their stake but also impersonate them. Done at scale, this could enable reorganisations of the Ethereum chain itself. This validator risk threatens Ethereum’s ability to agree on what’s true. When you lose the ability to agree on whats true, trust disappears.
On-Setup Attacks
Ethereum’s complexity also opens an additional attack category which isn’t present on Bitcoin.
Many protocols are initialised using a one-time ceremony that produces fixed public parameters baked into the protocol’s foundation.
A CRQC only needs to attack those parameters once. After that, the backdoor is permanent and can be exploited by a classical computer.
Tornado Cash is the clearest example. It’s a privacy protocol that processes transactions anonymously. Its anonymity guarantee rests entirely on parameters set during a one-time initialisation ceremony.
A single quantum computation against those parameters would permanently break the anonymity of every transaction ever processed through it and allow the protocol to be drained.
7. The Migration Problem
Post-quantum cryptography (PQC) exists. Algorithms that are believed to be resistant to quantum attacks have been developed, standardised, and in some cases deployed. NIST finalised its first PQC standards in 2024.
Getting them into widespread use is a different problem.
The Technical Problems
The leading post-quantum replacements produces signatures significantly larger than existing signatures.
Larger signatures mean fewer transactions per block, slower throughput, and significantly higher costs across the entire network. The performance tradeoff matters at scale.
PQC signatures are also relatively new. The algorithms exist, but their deployment in blockchain systems is still early. Performance, software implementation, and edge cases are still being worked through in real time.
The Consensus Problems
Even if the technical solution were mature, decentralised networks can’t be as easily updated as centralised systems can. Bitcoin requires consensus across developers, miners, exchanges, wallet providers, and millions of individual users before any changes can be made.
Bitcoin has hard-forked over smaller disagreements. The 2017 block size war took years, split the community, and produced Bitcoin Cash. A migration to PQC would be one of the most consequential changes in Bitcoin’s history.
BIP-360, the current proposal for a quantum-resistant script type, has a testnet, and has serious support. It also has serious opposition as introducing larger signatures would reduce the number of transactions that could fit in a block, slowing the future transaction rate.
The Migration Window
For active wallets, in principle the path is straightforward: migrate to a quantum-resistant address before a CRQC arrives.
The problem is timing. Migration requires network consensus, protocol upgrades, wallet software updates, and individual user action across millions of addresses. That process can take years.
For Bitcoin specifically, the migration would take months even using all available blockspace for just these transactions. 5
The window is still open but is narrowing, and the governance process required doesn’t move at the speed the threat is moving.
What’s Already Happening
Some chains have moved. The Quantum Resistant Ledger was built on PQC from the start. Algorand, Solana, and the XRP Ledger have made early experimental deployments. Ethereum has an active post-quantum roadmap. These are proof points that migration is technically possible.
But these are all early. The chains with the most to protect are the ones with the least ability to move quickly.
8. The World’s Largest Treasure Hunt
ECC doesn’t only protect crypto wallets. It protects internet traffic, banking systems, secure messaging, electronic passports, and government communications. Everything digital that matters. All have the same lock with the same vulnerability.
The treasure hunt is about the entire digital security architecture of modern society. Crypto is just the most visible and most immediately quantifiable target.
The hunt is already underway. Nation states and sophisticated actors are harvesting encrypted data today, intercepting and storing communications and financial records they cannot yet read. When the machine is built, they will decrypt everything they have collected. The CRQC doesn’t need to exist yet for the collection to start.
The Permanent Problem
Migration only works for active wallets. For a significant portion of the assets at risk, there is no migration path at all.
Around ~2.3 million BTC cannot be migrated.This includes wallets whose owners are gone or where the keys are almost certainly lost. The coins cannot be moved to safety.
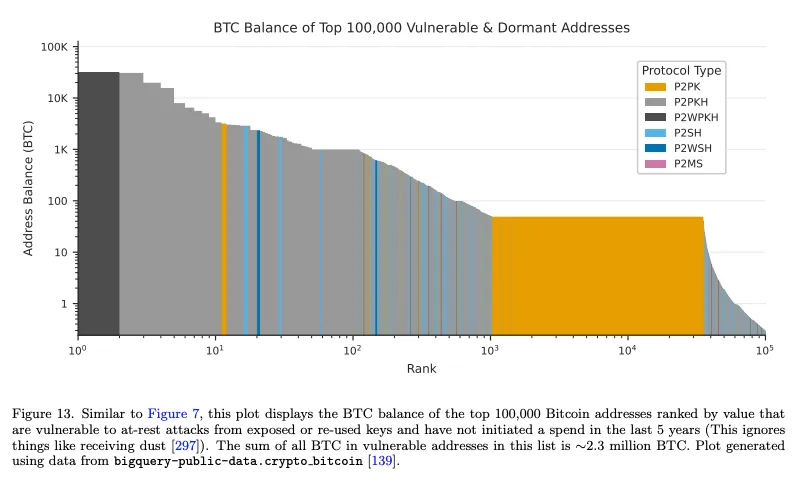
These are fixed targets. Whoever is first to build a CRQC can be the first gets to collect.
The Geopolitical Dimension
The stakes are now large enough that governments have started paying attention.
The race to build a CRQC also involves nation states with active classified quantum programmes that don’t publish their progress. The paper explicitly highlights this: the first CRQC may never be announced, it’s existence may only first be detected on the blockchain.
The paper recommends governments treat this as a national security issue. An adversarial state can quietly drain hundreds of billions in digital assets into permissionless wallets, evading any sanctions that may exist in the traditional financial system
But as discussed, the problem is even bigger. Once a CRQC capable of attacking Bitcoin is built, the blast radius is much larger. The same encryption underpins every secure communication a government has sent, every classified document it protects and every financial system it governs. That’s why this is a national security issue.
What the Crypto Community is Debating
The Bitcoin community knows the problem. Agreeing on what to do about it is another matter.
Three positions have emerged, and none has won.
Do nothing: Property rights are inviolable, and the protocol should not confiscate assets under any circumstances. The issue is that the price will likely be impacted negatively.
Burn: Destroy the vulnerable coins before a quantum attacker can take them. Remove the incentive, protect the network, prevent the shock. The objection is that burning coins with possible living owners is confiscation, and it sets a precedent for what the protocol can do to assets it decides are inconvenient.
Hourglass: Rate-limit spending from vulnerable addresses and create a managed migration window. Owners race to move their coins within the allowed rate, fees flow to miners, and the attack surface shrinks gradually. The dynamics are messy and the window may not be long enough, but it avoids both the supply shock and the confiscation question.
An informal poll at the 2025 Presidio Bitcoin Quantum Summit recorded roughly equal support for all three. If nothing changes, the protocol won’t move.
The Bad Sidechain
The paper proposes a fourth option.
It maps it directly against the bad bank mechanism used during financial crises. When toxic assets threaten the whole system, you quarantine them.
Applied to Bitcoin, the proposal is a recovery sidechain where claims on dormant assets can be submitted and verified. Ownership would be established and verified offchain, with coins returned to rightful owners in an orderly way rather than lost to whoever builds the machine first.
The paper calls this digital salvage. Regulated recovery, like maritime salvage law, that brings the assets into the formal economy rather than letting them fall to an adversarial actor. Governments create the rules and let regulated entities run the recovery. The gains come back into the taxable economy.
It is technically hard and politically contentious. It asks the Bitcoin community to accept something that looks, from certain angles, like exactly the kind of intervention Bitcoin was designed to prevent.
But doing nothing is also a choice. Without a framework, whoever gets there first keeps everything.
9. What Happens Next
We started with a teaser, that underneath the technical complexity of Google’s paper is a story about hundreds of billions of dollars in digital assets that will become accessible to whoever builds a specific machine first.
Having walked through the paper, you can now see the full shape of that story.
The lock protecting every crypto wallet has a hidden mathematical structure. Shor’s algorithm finds it and extract the private key. Google’s paper showed a major advance that brought forward our estimates of when that could happen by an enormous amount, a ~20x reduction in the resources required.
Google's paper didn't arrive alone. Oratomic published results on the same day showing parallel advances on a completely different hardware architecture.6 Multiple research groups are converging on the same destination.
That is what major jumps in progress look like.
Two curves are closing simultaneously, our ability to build more qubits rising while the number required to break our encryption keeps falling. Building a machine powerful enough to perform quantum attacks is moving from sci-fi to an engineering problem.
The targets are already publicly visible on chain and the prize grows with every asset that moves onto these rails. This is now a race that includes nation states with classified programmes, and their progress isn’t public. The paper warns the first CRQC may never be announced and we may not know the race has been won until the coins start moving.
This is a window of existential threat for the entire existing crypto ecosystem. How it responds will define whether digital assets can be the future of financial infrastructure.
The largest treasure hunt in human history is already underway. The map is drawn. The machines are being built. The actors shaping what happens next include some of the most powerful entities on earth.
It’s a race against time that most people still don’t know is happening. Now you do.
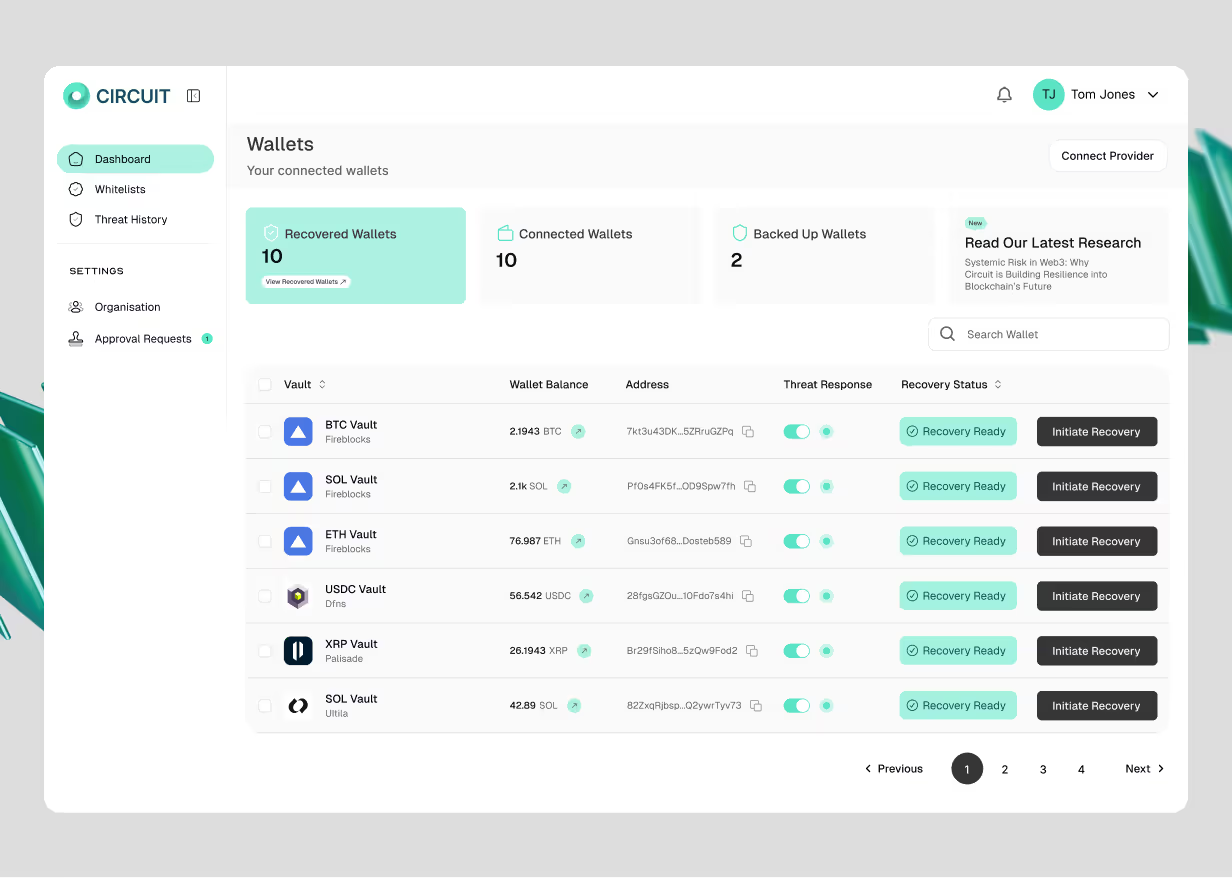
A note on Circuit
We’ve been thinking about private key compromise as an operational risk long before this paper was published. Quantum accelerates the timeline, but the underlying problem, that when a key is compromised, the window to respond is shorter than any human process can match, isn’t new.
Circuit builds infrastructure for that scenario. Pre-approved and pre-signed transactions that automatically move funds to safety when a key is at risk, without waiting for manual intervention. It addresses one of the most immediate problems.
Circuit is backed by Lloyd’s of London and recognised by 10+ major insurers as an enterprise risk control that reduces premiums. If you’re thinking about how to protect digital assets against key compromise, we’re here to talk.
Want to keep up to date with Circuit? Sign up below
Related Posts
Discover more about Circuit’s latest News and Research
Inside the Kelp/LayerZero Hack: How Lazarus Forged $292M Into Existence
A single lie, six layers deep, and the cascade that pulled in every major lending protocol on Ethereum. A forged cross-chain message led to a $292M exploit draining Kelp and cascading into Aave and DeFi. This breakdown shows how one failure propagated across Ethereum.

$285M Drift Hack Breakdown
A single lie, six layers deep, and the cascade that pulled in every major lending protocol on Ethereum. A $285M DeFi hack executed in 12 minutes after 6 months of social engineering. This breakdown shows how Drift was compromised and what it means for crypto security.

The US Crypto Regulatory Convergence: What Compliance Teams Need to Know Now
Every major US federal financial regulator has moved to enable institutional crypto. The OCC's 376-page GENIUS Act rulemaking is the most operationally detailed framework yet, covering reserve requirements, redemption mechanics, custody standards, and operational resilience. We break down what the proposed rules require, where the compliance pressure points sit, and what operators should be doing before the comment period closes on May 1, 2026.
Built by experts who’ve made digital assets safer, and now, recoverable
We believe asset recoverability is table stakes for the next era of digital assets.





